10 Facts You Never Knew in 2022: Must-Know Cyber Attack Statistics And Trends in New York
10 Facts You Never Knew in 2022
In 2020, cyber attacks ranked as the fifth greatest danger. Now it has established itself as the standard in both the public and private sectors. Some studies predict that this risky industry will keep growing in 2022 as IoT cyberattacks continue to rise by 2025.
The COVID-19 epidemic has caused a 600% increase in cybercrime, which encompasses anything from theft or embezzlement to data hacking and destruction. Every industry has had to adopt new technologies, which has compelled businesses to act rapidly to adapt.
Many firms conduct daily operations, including cybersecurity. It is a significant rise in data breaches and hacks from sources increasingly widespread in the workplace.
Smartphones and IoT devices lack data security, worldwide pandemic impacts, and growth in exploit complexity. Additionally, COVID-19 has increased the use of remote workers, paving the way for cyberattacks.
What are Cyber Attacks, and why are they getting worse?
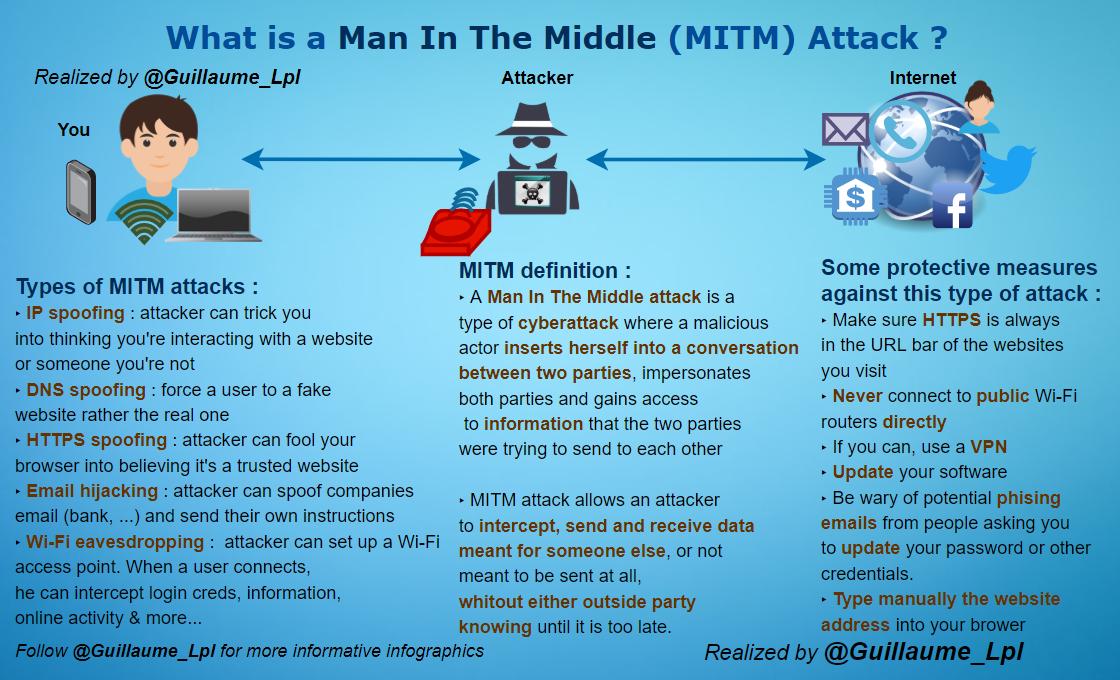
An assault carried out by online criminals using one or more computers on one or more computers or networks are known as a cyber attack. There must be much more education about the risks to consumers and businesses to lessen the broad suffering and disruption caused by cyber catastrophes.
Cyber assaults against all types of organizations, but especially against small and medium-sized ones, are increasing in frequency, specificity, and complexity. In addition to disrupting routine business activities, a cyber assault may harm critical IT infrastructure and assets, which might be hard to repair without the necessary funding or resources.
What is Cyber Security?
Cybersecurity is the defense against harmful assaults by hackers and cybercriminals against internet-connected devices and services. Firms employ the procedure to protect themselves against phishing scams, ransomware attacks, identity theft, data leaks, and monetary losses. [1]

It deals with ways to protect systems and services from malicious online attacks by spammers, hackers, and other cybercriminals. While specific cyber security components are built to launch an assault immediately, most modern specialists are more concerned with safeguarding all assets, from computers and cell phones to networks and databases, against attacks.
How Can the Risk of Cyber Attacks Be Reduced?
The best action is to implement measures to prevent data security breaches. It gives the growing risks that hackers could misuse your data second only to getting sufficient professional data breach insurance. There are distinct considerations based on your organization’s location because state-by-state data breach regulations change.
Cut back on data transfers
Because more workers are doing remote work, it is frequently necessary to transfer data between work and personal devices. Sensitive data held on personal devices dramatically increases the danger of cyberattacks.
Boost password safety
The first line of protection against several assaults is the password’s strength. Protecting your sensitive data requires using passwords made up of random symbols, changing them frequently, and never writing them down or sharing them with anybody.
Surveillance of data leaks
Long-term data leakage can have adverse effects, but they can be lessened by regularly analyzing your data and locating existing leaks. Data breach monitoring systems keep a close eye on any unusual behavior and immediately notify you.
Download with caution
If you download files from unreliable sources, your systems and devices may be vulnerable to security concerns. It’s essential only to download files from reliable websites and avoid illegal downloads to reduce the possibility of malware infecting your computer.
What are the main reasons behind Cyber Attacks?

You can strengthen your defenses and be ready for anything the threat landscape throws your way if you can better grasp some of their motives and who is most likely to target your particular company.
Political Purpose
Several cybercriminal organizations target significant corporations using their hacking prowess. Most of the time, they are motivated by a specific goal, such as increasing public awareness of human rights concerns or alerting a big corporation to system vulnerabilities. They could also face up against organizations whose views differ from their own.
Financial Success
A hacker’s primary driving force is money, and there are several ways to acquire it. They could gain access to a bank or investment account directly, steal the password to your financial websites and then transfer the assets to one of their own. They use a sophisticated spear phishing scheme to trick an employee into sending money, or they could launch a ransomware attack against your entire business.
Fame Game
The sense of accomplishment and fame that comes with breaking into a vital system drives some hackers. While some people may work alone or in teams, they want to get fame on some level. It has to do with the notion that cybercriminals are competitive individuals who take pleasure in the challenge that their actions create. They frequently encourage one another to perform trickier hacks.
10 Facts You Never Knew About Cyber Attacks
- According to the ANSSI, ransomware attacks against enterprises increased by 255% in 2020 compared to 2019.
- Most American businesses impacted by the hack have declined to complain. The remaining 50% are ready for impending hacking assaults. Remember that studies and statistics often only include instances of fraud that they verified.
- The FBI received 19,369 reports of business email breaches or email account compromise online crimes in 2020, a growing percentage involving identity theft and money conversion into cryptocurrencies.
- Any unintended user activity (or inaction) resulting in a security breach is a human mistake in the context of digital security. These acts are not limited to downloading dangerous attachments and using generic or weak passwords.
- According to the most recent Cisco/Cybersecurity Ventures report, the cost of cybercrime seems to reach $10.5 trillion by 2025.
- Manufacturing enterprises are the target of about 25% of ransomware attacks. Governmental organizations and companies that provide professional services follow it.
- There are a lot of insecure applications available in the Google Play Store. Utilizing these applications runs the risk of identity theft, financial ruin, and data loss.
- Companies expressed worry about cybersecurity threats related to remote work in four out of five cases.
- In 2021, over 46 million websites will be using SSL by default, and as SSL usage increases and becomes more critical for SEO, more websites will buy SSL certificates.
- Hackers discover that many small firms haven’t made sufficient investments in cyber security and wish to take advantage of these weaknesses for financial gain or to express their political views.
Cyber Security Statistics And Trends in New York
These fascinating cyberattack stats only serve to underline the might of hackers. Whose organized networks continue to expand. Private and governmental organizations need to be stricter and concentrate on understanding best practices to guard against this.
Data Leak
This type of assault typically prioritizes the human element above the IT infrastructure. It is considerably simpler to convince someone to install spyware without understanding their error than searching for technological flaws. Phishing tactics will therefore be widespread in 2022.
Mobile apps and devices
Even with a good hand in 2022, mobile gadgets remain an accessible target. In 2020, 97% of businesses will deal with mobile attacks employing numerous attack channels, according to research from Check Point. Not to add, the attack surface has grown due to the remote operation. Every gadget in use provides a point of entry.
Targeted apps and services will become (very) profitable thanks to 5G and IoT., a pattern that Gartner and McAfee-Fireeye identified. In general, teleworking is a massive problem for security firms and necessitates a giant fusion of current security systems.
Social media accounts
Cyber attackers will continue to be used by cybercriminals to create fake profiles and enter businesses. Mass phishing or fraud will continue from misinformation and false news efforts. It was demonstrated to us this year with the bogus vaccination certificates.
Phishing
It is a type of cyberattack that makes use of spoof emails. The attacker’s objective is to persuade the receiver that they have received essential communication from their bank or corporation, for example, and that they must click on a link or download anything. Hackers exploit the data they have collected to put malware on crucial systems.
Data violation
Hospitals and cybercrime statistics indicate that financial firms are not the only ones who experience data breaches. The healthcare industry has always been one of the most targeted. Up to 550 healthcare firms in the US reported data breaches in 2021. These cyberattacks impacted over 40 million people because they took patient privacy information.
Cloud
Although the cloud has numerous advantages, it is becoming more and more standardized. Cybercriminals benefit from this since it makes it easier for them to test their assaults against strictly standardized answers. Additionally, the cloud’s flaws open the door to large-scale assaults.
Ransomware assaults
Ransomware is a category of malicious software that targets computers [2]. The system then displays notifications requesting payment from the user to resume operation. It’s an illicit money-making scam, and nations with large populations of internet users, like the United States, are more vulnerable to this sort of security issue. According to current statistics on ransomware, 18.2% of all assaults were in the United States.
Cryptocurrencies
Cybercriminals are targeting crypto as it continues to gain prominence and is in high demand worldwide. It’s like a personal invitation for hackers with the rise of asset holders, bitcoin wallet management programs, and transactions.
How Does Cyber Security Perform?
The technologies, procedures, and techniques used in cyber security protect networks, data, and computer systems from intrusion.
Cloud Safety
Cloud security is concerned with developing safe cloud systems and applications for businesses that employ cloud service providers like Amazon Web Services, Google, Azure, Rackspace, etc.
Software Security
Application security refers to the integration of various protections against a variety of threats into the software and services of an organization. This subdomain requires cyber security professionals to create safe code, build secure application structures, implement strong data input validation, and more to reduce the possibility of unwanted access or manipulation of application resources.
Mobile Protection
Mobile security is becoming increasingly important as more people rely on mobile devices. The subdomain helps against dangers, including illegal access, viruses, and more for corporate and individual data on portable devices like tablets, smartphones, and laptops. Mobile security also makes use of authentication and training to strengthen security.
Network Protection
Hardware and software defenses against interruptions, illegal access, and other abuses are network security—effective network security guards against various dangers from inside or outside the company.
Data Protection
This subdomain includes the procedures, protocols, and mechanisms that allow authorized users’ authorization and authentication to access an organization’s information systems. These procedures entail implementing robust information storage systems that protect the data in transit or stored on a server or computer. Additionally, this sub-domain employs two-factor or multi-factor authentication techniques more frequently.
Why are data on cybersecurity safety and governance crucial?
Particularly for businesses with remote employees, the dangers of not safeguarding information are more common and severe than ever. As stricter laws preserving data privacy are passed in regions worldwide, governments should apply more harsh penalties.
As additional nations worldwide are anticipated to adopt the law, businesses should be aware of the GDPR’s lessons. It’s essential to configure file permissions correctly and delete outdated data for security.
Maintaining compliance with data privacy laws like HIPAA, SOX, ISO 27001, and others requires maintaining data categorization and governance standards.
Conclusion
Organizations need skilled cybersecurity specialists who can use cutting-edge cyber tools to battle and eradicate possible risks, data breaches, and cyber-attacks to keep up with the rapidly evolving business dynamics.
However, the lack of easily accessible individualized learning modules that employees can access from any location at any time is the main obstacle that most firms encounter when trying to upskill their workforce.
The main issue for digital enterprises throughout the world has always been cybercrime. Companies’ reliance on technology for innovation and expansion opens them with more opportunities for cybercrime problems. To more successfully choose your cyber protection strategies, you must be aware of the statistics.
FAQs
Q.1: What makes cyber security crucial?
Your business may be badly disrupted and damaged by cybercrime. Attacks subject your company to failing to fulfill contractual obligations, financial damages, and a damaged reputation.
Q.2: What cyberattacks will be the most prevalent in 2022?
The most frequent attack method is still credential theft (19%), followed by phishing (16%), improper cloud configuration (15%), and flaws in third-party software (13%).
Q.3: How many cyberattacks will occur per day in 2022?
However, since there are about 2,200 intrusions every day, it can translate to over 800,000 people being affected annually.
References
- [Cyber Security] From CISA Link: https://www.cisa.gov/cybersecurity
- [Mitigating malware and ransomware attacks] From NCSC Link: https://www.ncsc.gov.uk/guidance/mitigating-malware-and-ransomware-attacks